
Earlier this week, Zimperium zLabs discovered malware that has been distributed to over 200 android mobile applications by dodging the Google Play stores security verification process. According to the report, this Android malware was categorized specifically as a trojan and could disguise itself behind premium mobile services. This trojan was then able to infect over 10 million victims spread across 70 countries. They estimated the total amount stolen to be in the hundreds of millions of Euros. The researchers believe that the hackers behind this trojan have hit so many devices that a stable recurring revenue of illegal funds has been established. While most premium service scams use phishing methods, this attack utilizes a trojan hidden embedded within android applications, which capitalized on the victim’s interactions for a larger and more widespread infection.
The zLabs report has named the trojan “GriftHorse” and claims the malware campaign has been active since at least November 2020. GriftHorse has targeted victims across 70 countries by sending malicious pages to users based on their IP addresses. These malicious Android apps initially appear harmless to victims even when reviewing their description and requested permissions. However, those who download the applications are continuously charged for monthly premium services that they subscribed to without their consent. This campaign relies on victims divulging their mobile numbers, which is used to subscribe them to premium SMS services. The trojan is embedded within a wide variety of Android apps which can vary from entertainment, lifestyle, puzzle games, and dating apps. The most popular malicious app being a translator, which at the time of the report, has over 500,000 downloads
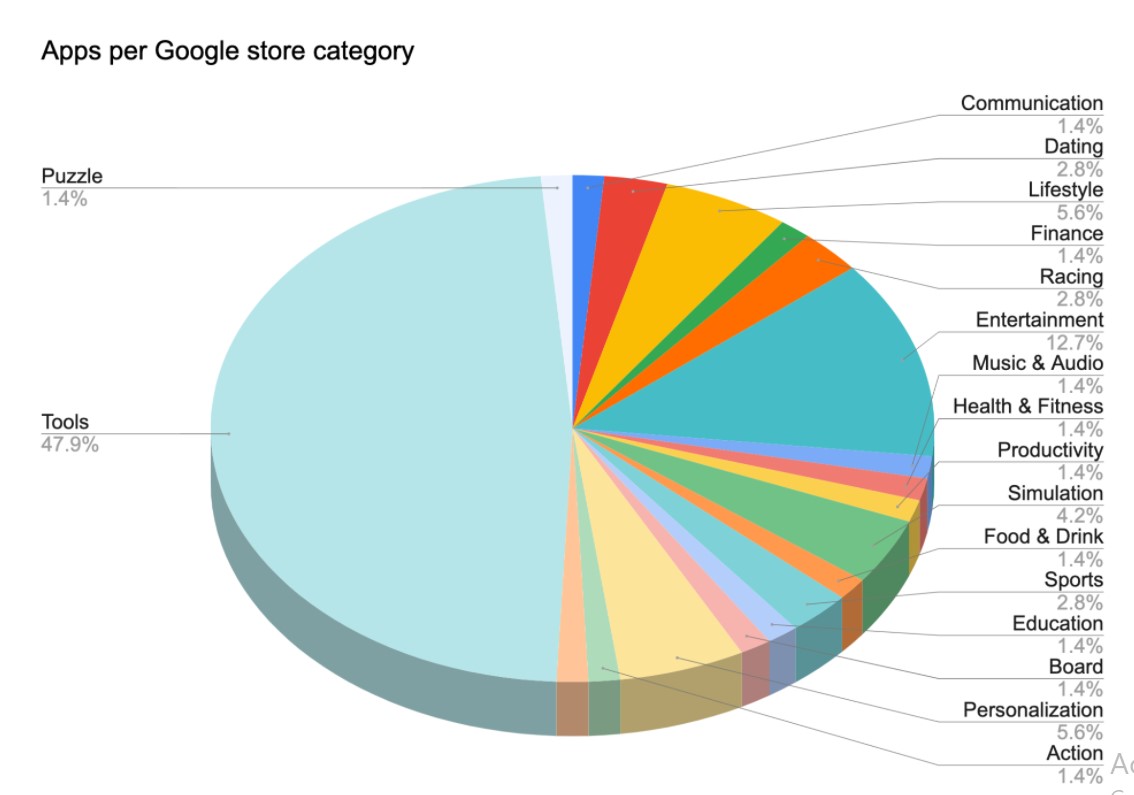
Figure 1- Source: Zimperium zLabs
Once installed, GriftHorse bombards the victim’s device with messages regarding a prize that they need to claim immediately. The sense of urgency often tricks users into following through with the prompts. The victims are then asked to share their mobile numbers for verification purposes. The number they submit is used to subscribe them to premium services. The victim does not immediately realize they have been scammed, so it is often too late before anyone realizes that they have been tricked. Therefore, the chances of obtaining a refund of their lost money are low.
To minimize the risk of discovery the malware’s creator avoided using statically defined URLs. GriftHorse has a high success rate benefitting from the local trust, misinformation, and small screens to scam users into downloading and installing malicious android applications. The report’s findings were shared with Google, who verified the data and immediately removed the malicious applications from the play store.
For more news and updates, visit https://blog.excellimatrix.com/
You can also reach out to us on Facebook, & LinkedIn or Contact us directly