
According to researchers at Proofpoint, a phishing attack is using public concern over the Omicron variant of COVID-19 to steal credentials and gain access to user accounts at several US universities. Cybersecurity researchers have identified an uptick in email threats targeting primarily North American universities to compromise university login credentials. The report suggests that hackers were seen leveraging Omicron’s concern, which is believed to have started in October but has become more evident in late November. In the last two years, cybercriminals have been hiding behind COVID-19 fears to carry out their phishing activities.
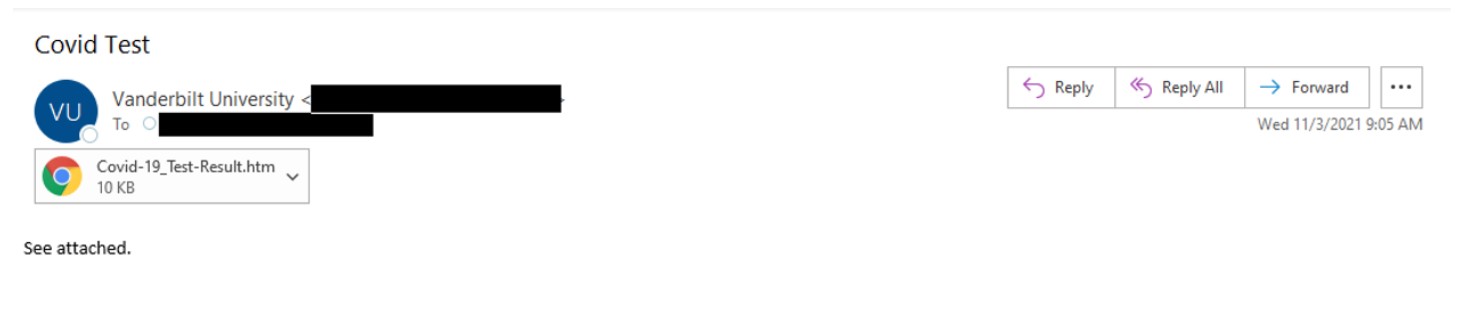
Attackers are spoofing the login pages for universities like the University of Central Missouri, Vanderbilt University, and more. Some portals resemble Office 365 login portals while others use convincing creations of the actual university pages. Researchers at Proofpoint believe such attacks will increase in the coming months as universities welcome back students after the upcoming holiday season.

Source- Proofpoint
In some cases, the phishing emails contained URLs, or attachments, for pages designed to store user credentials for university accounts. Then the user is redirected to the original university login page after they harvested their login information. The emails come with urgency or call-to-action subject lines such as “COVID test” or “Attention Required- Information Regarding COVID-19 Omicron Variant-November 29” to maximize the likelihood of collecting their data.
Source- Proofpoint
Proofpoint researchers have identified several threat clusters leveraging COVID-19 to attack universities using different techniques, tactics, and procedures. In addition, researchers have observed the use of both attachments and URLs in phishing campaigns. Hackers not only use several delivery methods but also use different sending and hosting methods to distribute the campaigns.
In some campaigns, hackers have attempted to compromise multifactor authentication (MFA) credentials, mimicking Duo, an MFA provider. With the help of stolen MFA tokens, the attackers could bypass the second layer of security designed to keep out these malicious actors.
Proofpoint in its official report suggests that while hackers sent many phishing messages from illegitimate email addresses, they have also used authentic compromised university accounts to attempt to phish other students and staff. The researchers also believe the threat actors are stealing students’ credentials and using compromised mailboxes to send similar threats to other US universities.
For more news and updates, visit https://blog.excellimatrix.com/
You can also reach out to us on Facebook, & LinkedIn or Contact us directly